RIT Phish Bowl
Report a Phish
If you receive a suspicious email, and it is not already posted here,
please report it using the built-in reporting tools in Outlook or Gmail.
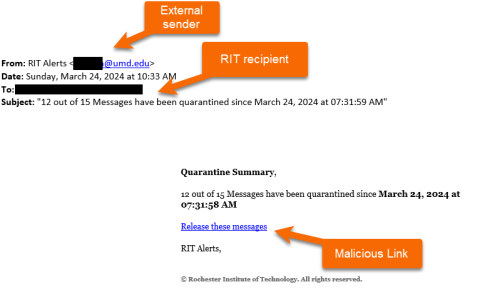
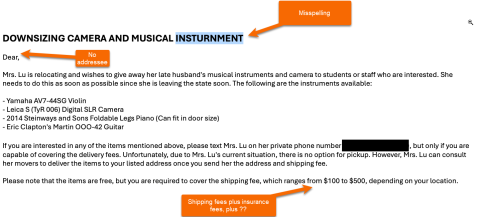
For detailed instructions on when to unsubscribe, report spam, or report phishing, and how to verify senders and links, see KB0045448: When and How to Unsubscribe, Report Spam, or Report Phishing and How to Spot Spoofing & Bad Links.