Spear Phishing
- RIT/
- Security/
- Resources/
- Types of Threats/
- Phishing/
- Spear Phishing
Spear Phishers Exploit Trust
Spear phishing is an email that appears to be from an individual or business you know. Phishing attacks are broad and target everyone, spear phishing attacks are targeted and specific, making them trickier to spot. Spear phishing emails can target large groups, like the Hilton Honors members, or small groups, such as a specific department or individual. Spear phishing emails can address an individual specifically and can even contain information that makes it look real and valid, such as information that may only pertain to you or a specific audience. They can contain links to official looking websites, but it's important to remember that university branding on a website does not mean it's official!
Spear phishing is a more targeted version of phishing, but the goal is the same. Cyber criminals want your money and your private information. With spear phishing, they may even attempt to use the company or organization you work for to dupe you into wiring money or giving out confidential information. Using information that can be found online, including your social media profiles, attackers can create personalized emails impersonating people you trust. A spear phishing attempt can be very convincing especially when it seems to be from a trusted contact such as your boss.
Examples of Spear Phishing
- Fraudsters pose as your bank’s IT services asking you to make a “test” transfer to ensure that your account is working.
- An attacker impersonates a high-level executive such as the boss or president of an organization. They use this influence to convince your organization’s accountant to transfer money to a bank account.
- A spear phishing email has a link or attachment that, when clicked, installs malware on your machine, giving a cybercriminal access to your organization’s network.
- An email from someone such as a network administrator asks you to log into a web page that requests your employee username and password.
Spear Phishing Facts
- Small businesses (1-250 employees) and very large businesses (2500+ employees) are common targets for spear phishing
- Attackers are using stolen email accounts from one corporate victim to spear-phish victims in higher management positions
- The file extensions .doc and .exe are two popular forms of attachments in spear phishing emails
- The precision of spear phishing attacks is increasing, meaning less malicious emails have to be sent in order to be successful
- Spear phishing emails usually appear to come from a trusted source
In order to decrease your chances of being a target of spear phishing, make sure you are keeping your information private. Take a look at your web presence including social media profiles. Are your accounts set to private? Do you have information on your profile that can be viewed by anyone? Make sure that you are not publicly displaying your birthdate, email addresses, employer information, or userIDs. Also, do not post such things on your page or a friend’s page.
Despite being trickier to spot, there are still some signs to identifying a spear phishing attack. Let's take a look at one and identify some of the key indicators.
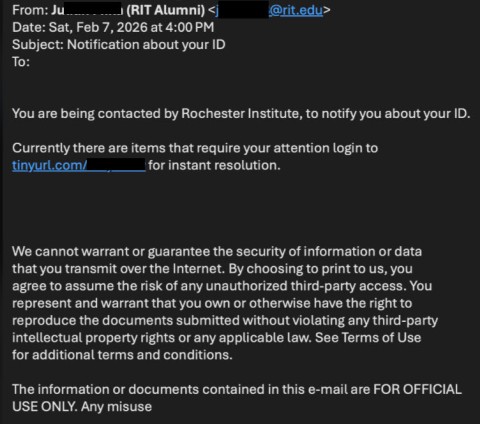
You'll notice that the sender on this message was an RIT email, and it's not from an official RIT office.
Another strong indicator is the lack of an addressee.
The last sign, and key indicator, is the tinyURL link.
If you happen to fall for a spear phishing attack and give out information or click on a link please follow these steps: send a copy of the email to spam@rit.edu, delete the phishing email, change your password, and scan your system for viruses and spyware. Report the situation to your Help Desk (Resnet, SCOB, NTID, ITS) as soon as possible.
For additional resources and information please check out:
- What is Spear Phishing? https://www.youtube.com/watch?v=9yHMKHlEKQ8
- RIT Information Security Identity Theft page: https://www.rit.edu/security/content/identity-theft
- RIT Information Security Phishing page: https://www.rit.edu/security/content/phishing
