Ph.D. student presents work at IEEE INFOCOM Conference
Geoff Twardokus, a student in the Ph.D. in Electrical and Computer Engineering program, presented his work “Vehicle-to-Nothing? Securing C-V2X Against Protocol-Aware DoS Attacks” on May 5, 2022 at the IEEE International Conference on Computer Communications (IEEE INFOCOM).
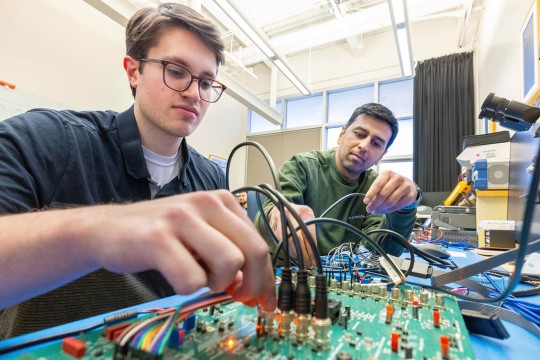
IEEE INFOCOM is widely regarded as one of the most reputed and selective conferences in communications, with publication standards that often exceed those of the top technical journals. Geoff’s work, conducted in collaboration with his doctoral advisor, Dr. Hanif Rahbari, at RIT’s Wireless and IoT Security and Privacy (WISP) lab, investigates cyber-attacks on the 5G Cellular Vehicle-to-Everything (5G C-V2X) communication protocol. The 5G C-V2X protocol is quickly becoming the dominant technology for direct communication between moving vehicles and can be used for multiple applications, including automatic collision prevention. Geoff’s work is rigorous in studying cybersecurity attacks on the 5G C-V2X 5G Cellular Vehicle-to-Everything communication protocol both at the analytical level and with experimentation on practical realizations of the system on actual software-defined radios.
Learn more:
Paper abstract:
Vehicle-to-vehicle (V2V) communication allows vehicles to directly exchange messages, increasing their situational awareness and offering the potential to prevent hundreds of thousands vehicular crashes annually. Cellular Vehicle-to-Everything (C-V2X), with its LTE-V2X and New Radio (NR)-V2X variants in 4G/LTE- and 5G-based C-V2X, is emerging as the main V2V technology. However, despite security protocols and standards for C-V2X, we expose in this paper that its physical (PHY) and MAC layers are not resilient against intelligent, protocol-aware attacks due to the very predictable PHY-layer structure and vulnerable scheduling algorithm used in both LTE-V2X and NR-V2X. We devise two stealthy denial-of-service (DoS) exploits that dramatically degrade C-V2X availability, thereby increasing the chances of fatal vehicle collisions. We experimentally evaluate our attacks on an integrated, hybrid testbed with USRPs and state-of-the-art LTE-V2X devices as well as through extensive simulations, showing that within seconds, our attacks can reduce a target’s packet delivery ratio by 90% or degrade C-V2X channel throughput by 50%. We propose, analyze, and evaluate detection approaches as well as mitigation techniques to address the vulnerabilities we expose in the C-V2X PHY/MAC layers, providing direction towards better-secured, resilient 5G C-V2X.