Research

Research
- RIT/
- ESL Global Cybersecurity Institute/
- Research/
- Research Overview
Research with real-world impact
RIT cybersecurity researchers are conducting cutting-edge, award-winning research, sponsored by groups like the National Science Foundation and the Department of Defense. Through partnerships with industry and government, we are developing novel solutions and tackling the toughest problems in cybersecurity and artificial intelligence.
Meet some of our research community in our new video! You can also learn more about our Researchers by Area.
Our research initiatives bring together students and faculty from a variety of disciplines to drive real societal and economic impact. In addition, our commitment to undergraduate research means that these initiatives help to educate the next generation of cybersecurity professionals while they design and develop the technologies and systems needed to secure our future.
The Institute’s research agenda is powered by more than two dozen faculty across multiple colleges at RIT informing cybersecurity research with perspectives from engineering, psychology, public policy, and more.
Researchers by Area
Our research initiatives bring together students and faculty from a variety of disciplines to drive real societal and economic impact. In addition, our commitment to undergraduate research means that these initiatives help to educate the next generation of cybersecurity professionals while they design and develop the technologies and systems needed to secure our future.
The Institute’s research agenda is powered by more than forty across multiple colleges at RIT informing cybersecurity research with perspectives from engineering, psychology, public policy, and more.
Meet the Director

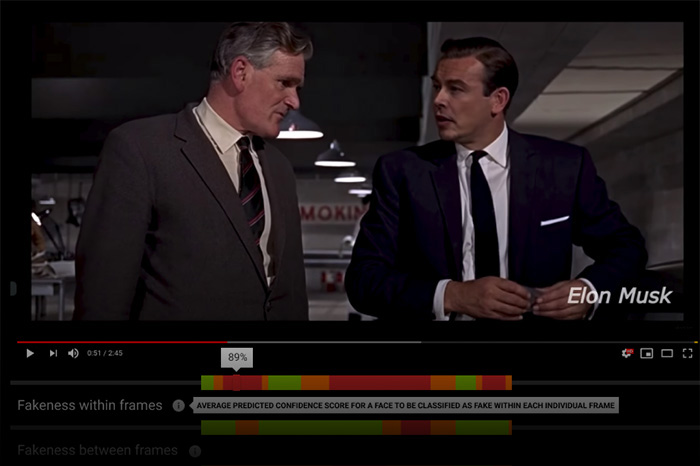
Today, ESL Global Cybersecurity Institute researchers are making communication networks, information sources and software development more secure. We are utilizing artificial intelligence and machine learning to protect our infrastructure, and discovering new frontiers in cybersecurity every day.