RIT researchers help develop practical new method for measuring quantum entanglement
Technique can help advance quantum computing and secure communication technologies
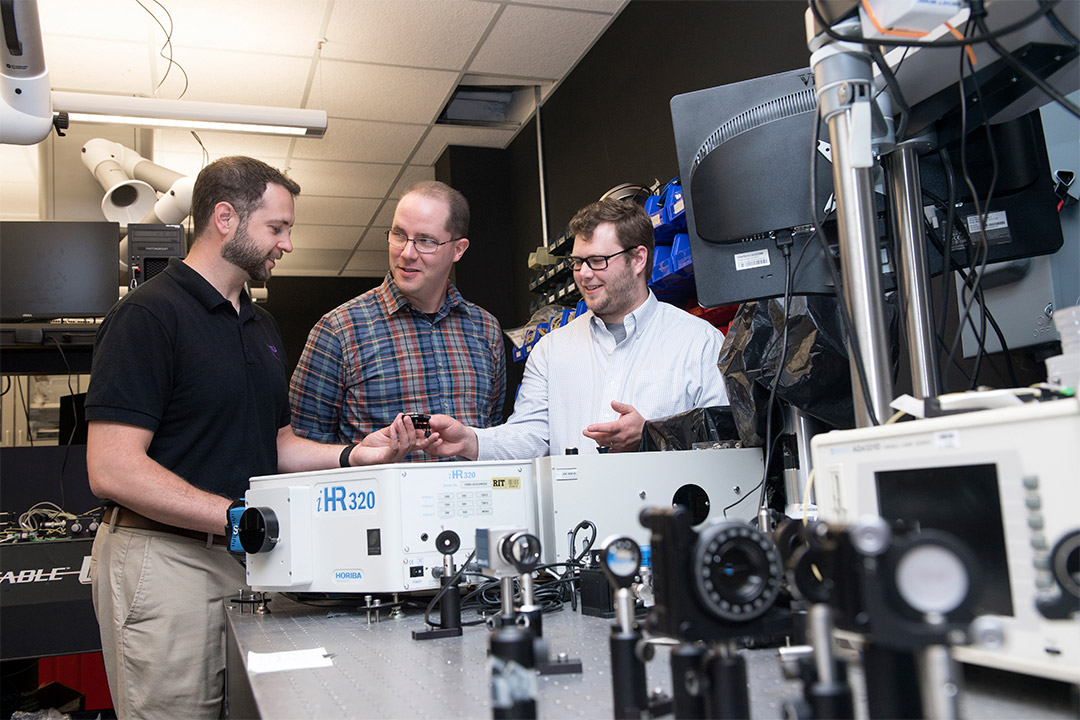
A. Sue Weisler
Michael Fanto (left), an RIT microsystems engineering Ph.D. student and the experimental lead for the Air Force Research Laboratory Quantum Information Science group; James Schneeloch (center), a postdoctoral researcher with the Air Force Research Laboratory U.S. Air Force; and Gregory Howland (right), RIT assistant professor, were among the researchers to develop a new technique to measure quantum entanglement.
Rochester Institute of Technology researchers have helped develop a new technique for quantifying entanglement that has major implications for developing the next generation of technology in computing, simulation, secure communication and other fields. The researchers outlined their new method for measuring entanglement in a recent Nature Communications article.
When two quantum particles—such as photons, electrons or atoms—become entangled, they have special correlations that show up in their measurements even when the particles are separated by an enormous distance. This unique property, which can only be explained through quantum mechanics, is at the heart of many of the technologies as part of the National Quantum Initiative.
“Quantum entanglement is a resource that can be used to do important tasks such as quantum computing or secure communication,” said Assistant Professor Gregory Howland, a member of RIT’s Future Photon Initiative. “Two people that have entangled quantum particles can generate an unbreakable key for sending messages back and forth to one another in such a way that if some third party intercepts the message, by the laws of physics it’s impossible for them to decode the message.”
As quantum technologies become more complex, users will need a way to calculate how much quantum entanglement exists within a given system. For the system in this study—involving spatially entangled photon pairs—the new technique needed a million-times fewer measurements than previous methods. And because the technique is based on information theory, the measurement technique has the added benefit of never overestimating how much entanglement is in a system.
“This turns out to be critical because it means we never accidentally tell you that you have more of the resource than you really have,” Howland said. “It’s especially important for something like secure communication, where you’re trying to avoid an adversary intercepting a message.”
The full article is available at https://www.nature.com/articles/s41467-019-10810-z.